Internet Security Essentials, also known as InternetSecurityEssentials, is a new fake antivirus program. Antivirus programs are used to remove viruses; however, since Internet Security Essentials is a fake antivirus program, it will not remove viruses. Internet Security Essentials is generally installed without user permission through the use of a trojan horse, which is downloaded through the internet. The trojan horse is generally downloaded when visiting specific websites. Internet Security Essentials was released first on the web in February 2011. However, Internet Security Essentials comes from the same family of viruses such as My Security Shield, Internet Antivirus 2011, and Smart Securty. Internet Security Essentials claims to provide firewall and antivirus protection. Some of the viruses which it claims to find include Trojan.BAT.AnitV.a and Trojan-PSW.VBS.Half.
Internet Security Essentials will generally modify the internet connection settings to not allow the user to access the web. The settings will be modified so that the user can only visit specific websites. In order to fix the issue, go to your internet explorer browser and click on Tools, Internet Options, Connections tab, and LAN settings. Next, uncheck the box by “Use a proxy server for your LAN (These settings will not apply to dail-up or VPN connections).”
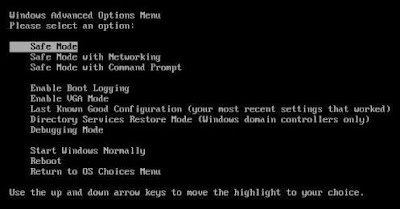
It is recommended to use safe mode when removing the virus because Internet Security Essentials will generally not be able to load in safe mode. To enter safe mode, restart the computer and press F8 multiple times before the Windows screen to bring up the boot options.
Manual Internet Security Essentials Removal
In order to manually remove Internet Security Essentials, the processes associated with Internet Security Essentials must be stopped, the files associated with the processes must be removed, and the registry entries must be corrected to the previous state before Internet Security Essentials entered the computer.
Important: Before attempting to manually remove Internet Security Essentials, we recommend that the user read through comments posted by other users on how they removed specific fake antivirus programs since many fake antivirus programs are similar. These comments can be found by clicking here. These comments may provide additional information which may be useful in removing Internet Security Essentials. However, please use discretion since these specific comments pertain to other fake antivirus programs.
Stop Internet Security Essentials Processes
[random].exe
Remove Internet Security Essentials Files
C:\Documents and Settings\All Users\Application Data\[random]\[random].exe
Remove Internet Security Essentials Registry Keys
HKEY_CURRENT_USER\Software\Internet Security Essentials
HKEY_LOCAL_MACHINE\SOFTWARE\Internet Security Essentials
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Security Essentials